Production companies are also digitally networked today - from the office to the machine.
DEFENDERBOX uncovers hidden security gaps and protects operational processes from unplanned IT disruptions.
The plug & play appliance or virtual machine ensures an all-round cyber-secure IT infrastructure!
The DEFENDERBOX regularly checks production IT, office IT and connected systems such as machine controls or IoT components for vulnerabilities - even in hybrid environments. The solution detects risks in outdated software, network access or configuration errors and provides clearly prioritized recommendations for safeguarding. The test intervals - daily, weekly, fortnightly or monthly - are based on your implementation speed.

Regular monitoring of network traffic enables early detection of anomalies and facilitates the investigation of security incidents.

DEFENDERBOX supports compliance with TSAX/ISO27001 with documentation of proactive cyber security audits.

Regular security checks monitor the increasing connection of production facilities to IT networks.
as with

Targeted checks on the Darknet for company data, compromised email addresses and passwords.

The DEFENDERBOX evaluations are tailored to the requirements of the management and the IT department: once short & crisp - once detailed & specific!

The DEFENDERBOX report contains precise recommendations on how to close the security gaps.

The security gaps found are prioritized precisely. This means you know which gaps need to be closed first.

All data is processed exclusively in Germany. None of your data will be stored.

DEFENDERBOX reporting is part of the statutory audits for NIS-2, DORA or ISO27001.

On-premise, multi-cloud, hybrid IT - the DEFENDERBOX moves seamlessly between environments.

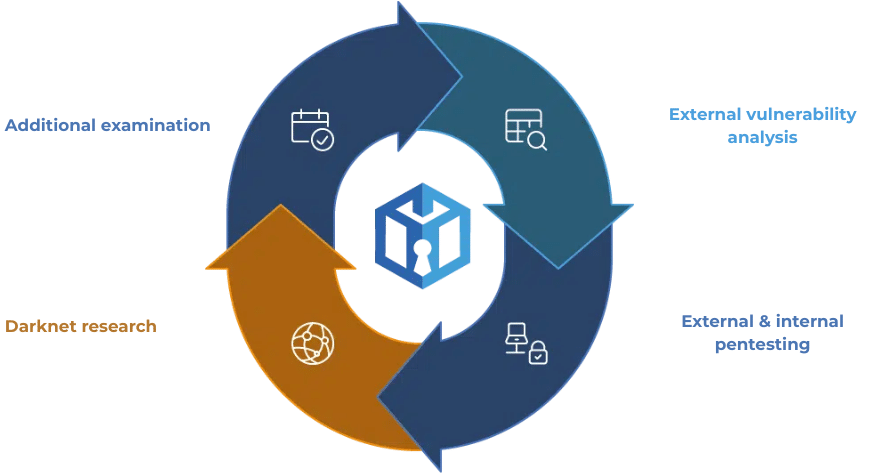
DEFENDERBOX's external vulnerability analysis systematically checks your IT infrastructure for security gaps and inefficient processes in order to identify risks at an early stage.

DEFENDERBOX's automated external pentest efficiently checks your external IT infrastructure for security gaps, assesses risks and continuously monitors security.


DEFENDERBOX's darknet research specifically investigates activities on the darknet, uses specialized tools such as Tor and checks email addresses for data leaks.
The DEFENDERBOX is a simple plug-and-play solution for IT security. As a Managed Security Service it checks your systems automatically and continuously - both from the outside and from the inside.

monthly with 100 IP's
applies to 100 IPs plus a one-off setup fee of €249
Everything you need to know - quickly, clearly and at a glance.
Yes, our DEFENDERBOX security checks can check industrial control systems for security vulnerabilities without disrupting production.
However, this is always carried out separately and in close consultation with you so as not to disrupt the production process if critical gaps are found.
Yes, DEFENDERBOX detects security gaps in networks and systems that could allow access to production data.
That is why the DEFENDERBOX is also suitable for companies with High compliance requirements, how
important - and interesting!
Yes, networked sensors and IoT devices are included in the DEFENDERBOX security checks to prevent cyberattacks on production.
The DEFENDERBOX provides detailed reports and Prioritized recommendations for actionthat you can import directly into your ISMS can be integrated.
This helps you to meet the requirements of:
✅ ISO 27001/2 | ✅ TISAX | ✅ DORA | ✅ DSGVO | ✅ NIS2
to fulfill - Fast, efficient and without additional effort.
Yes - Plug & Play.
The DEFENDERBOX is preconfigured and is ready for use in just a few minutes:
No specialist IT knowledge required!
The Intuitive dashboard (coming soon) also provides a complete overview.