DEFENDERBOX for NGOs
Cyber attacks are no longer only directed against large corporations. Non-profit organizations are also increasingly under attack, for example through phishing attacks on employees, ransomware attacks on servers and data, attacks on websites or donation platforms or security vulnerabilities in outdated software! Organizations with sensitive data in particular - for example in the areas of Health, education, development aid or social work - bear a special responsibility for the protection of this information.
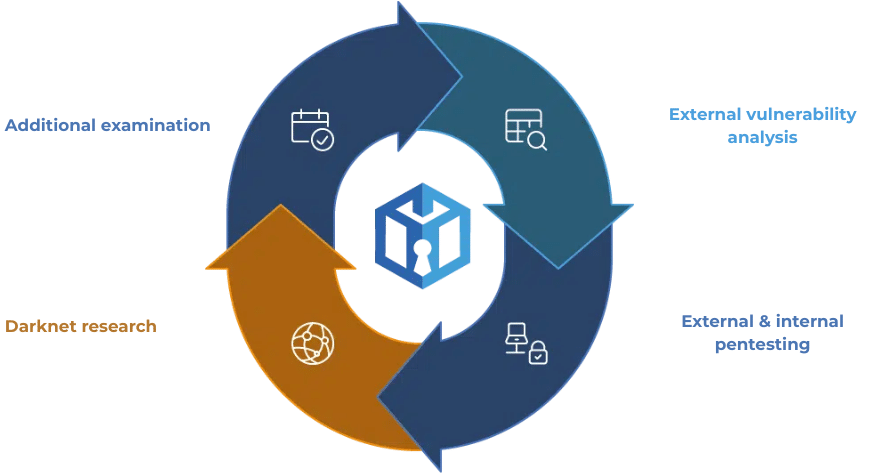
External & internal pentesting
External vulnerability analysis
Additional tests every 2-3 months
Darknet research
Protect your company!
The DEFENDERBOX protects NGOs where it really counts - for the data of your employees, donors and the people who support you. Our solution automatically checks your IT systems for vulnerabilities in compliance with data protection regulations and clearly shows you where risks exist and which steps really help.
This keeps your processes, donation platforms and sensitive information reliably secure - without additional stress for your team. The check intervals can be flexibly adjusted to suit your pace: daily, weekly, fortnightly or monthly.
After all, security is not a luxury, but a prerequisite for your organization to be able to continue its important work undisturbed. With DEFENDERBOX you can concentrate on what really counts: Your mission and the people you help.
At a glance
SIMPLE. FAST. CYBER SECURE.
Especially for NGOs
DEFENDERBOX supports, among others: Aid organizations, foundations, associations, educational organizations, development organizations, social institutions, small and medium-sized NGOs

Transparency & certainty of action
All security risks are clearly visualized. You know at all times, where there is a need for action, and can clearly prioritize measures - so your organization remains compliant and capable of acting even under NIS2, GDPR & Co.

Resource-saving security
Our solution is Plug & PlayNo complicated IT projects, no large teams required. Automatic checks and flexible intervals (daily, weekly, fortnightly or monthly) adapt to your day-to-day organization.

Prioritization & protection of sensitive data
DEFENDERBOX protects the information of your employees, donors and the people who support you. Security gaps are automatically detected, risks are prioritized and specific recommendations for action help to reliably secure data.
as with


Other components

DARKNET-
RESEARCH
Targeted checks on the Darknet for company data, compromised email addresses and passwords.

REPORTING
The DEFENDERBOX evaluations are tailored to the requirements of the management and the IT department: once short & crisp - once detailed & specific!

HANDLING
RECOMMENDATIONS
The DEFENDERBOX report contains precise recommendations on how to close the security gaps.

SMART PRIORITIZATION
The security gaps found are prioritized precisely. This means you know which gaps need to be closed first.

DATA SECURITY
All data is processed exclusively in Germany. None of your data will be stored.

COMPLIANCE REQUIREMENTS
DEFENDERBOX reporting is part of the statutory audits for NIS-2, DORA or ISO27001.

MANAGED SECURITY SERVICE
On-premise, multi-cloud, hybrid IT - the DEFENDERBOX moves seamlessly between environments.
Our range of functions

EXTERNAL VULNERABILITY ANALYSIS
DEFENDERBOX's external vulnerability analysis systematically checks your IT infrastructure for security gaps and inefficient processes in order to identify risks at an early stage.

EXTERNAL
PENTESTING
DEFENDERBOX's automated external pentest efficiently checks your external IT infrastructure for security gaps, assesses risks and continuously monitors security.

INTERNAL
PENTESTING
DEFENDERBOX's automated internal pentest efficiently checks your company network for security vulnerabilities, reduces costs and delivers reproducible test results.

DARKNET
RESEARCH
DEFENDERBOX's darknet research specifically investigates activities on the darknet, uses specialized tools such as Tor and checks email addresses for data leaks.
These industries rely on us:
Everything at a glance
This keeps your IT secure at all times - without any additional effort!
The DEFENDERBOX is a simple plug-and-play solution for IT security. As a Managed Security Service it checks your systems automatically and continuously - both from the outside and from the inside.
- Recognize security gaps immediately!
- Alarmed for new threats!
- Protects your company around the clock
1.
Plug in
2.
Scan
3.
Results

Prices
Base
Test installation
- One-time, automatic scan start
- External vulnerability scan
- External & internal pentesting 1 VLAN
- A little darknet research
- Basic Reporting
Test now for free!
Professional Subscription
- Continuous, automatic start
- Vulnerability analysis
- External & internal pentesting all VLAN
- Darknet research
- Complete reporting incl. certification (NIS-2, DORA, TSAX etc.)
- Additional tests
495€
monthly with 100 IP's
Professional One-time test
- Continuous, automatic scan start
- Vulnerability analysis
- External & internal pentesting all VLAN
- Darknet research
- Complete reporting incl. compliance certification (NIS-2, DORA, TSAX etc.)
- Additional tests
1.650€
applies to 100 IPs plus one-off setup fee of €249
Prices
Base
Test installation
- One-time, automatic scan start
- External vulnerability scan
- External & internal pentesting 1 VLAN
- A little darknet research
- Basic Reporting
490€
Professional Subscription
- Continuous, automatic start
- Vulnerability analysis
- External & internal pentesting all VLAN
- Darknet research
- Complete reporting incl. certification (NIS-2, DORA, TSAX etc.)
- Additional tests
495€
monthly with 100 IP's
Professional One-time test
- Continuous, automatic scan start
- Vulnerability analysis
- External & internal pentesting all VLAN
- Darknet research
- Complete reporting incl. compliance certification (NIS-2, DORA, TSAX etc.)
- Additional tests
2.490€
plus one-time 249€ setup fee
- Buy 10 - get 12
DEFENDERBOX
Special offer
- Buy a 10-month subscription, receive 12 months of scans
- Continuous, automatic scan start
- Vulnerability analysis
- External & internal pentesting all VLAN
- A little darknet research
- Complete reporting incl. compliance certificate
- Additional tests
FAQ about the DEFENDERBOX
Everything you need to know - quickly, clearly and at a glance.
Why does my NGO need cybersecurity?
Non-profit organizations are also targets of cyber attacks. Sensitive data of employees, donors and supporters must be protected. DEFENDERBOX helps to identify risks at an early stage and reliably secure data. without a large IT team.
How does DEFENDERBOX work for NGOs?
DEFENDERBOX automatically checks your IT systems for vulnerabilities and prioritizes risks. You receive comprehensible recommendations for action and a clear dashboard so that you can take targeted measures - Simple, fast and data protection compliant.
What are the inspection intervals?
The test intervals can be flexibly adjusted: daily, weekly, fortnightly or monthly - depending on how quickly your organization can implement changes. This keeps your IT continuously protected.
Do I need my own IT team to use DEFENDERBOX?
No. DEFENDERBOX is Plug & Play designed. You do not need your own security team. The solution is easy to integrate, delivers results automatically and supports you in the process, make safety-related decisions efficiently.
Frequently asked questions:
What is a penetration test?
A penetration test, or pentest for short, is a comprehensive security check for IT systems, networks or applications. We simulate real cyber attacks to uncover vulnerabilities and security gaps before they can be exploited by real hackers.
Difference between pentest and vulnerability analysis
In contrast to simple vulnerability analyses, our pentests or security scans go one step further: they actively exploit potential security vulnerabilities to test the system's resilience. This enables a realistic assessment of the security situation and uncovers vulnerabilities that may remain undetected with other methods.
How often should pentests be carried out
An initial pentest or security scan uncovers the most urgent security gaps. As the computer landscape continues to grow, even in small companies, the risk potential is also changing. Especially when servers and other security-relevant systems are connected to the Internet. For this reason, a weekly or at least monthly pentest is an essential part of a proactive security strategy.
Do the experts have to be on site or present during the security scans?
No, our experts do not need to be on site. You can do the simple installation of the DEFENDERBOX without us and the security scans are carried out completely remote. However, we will be happy to support you on site on request - this is possible for an additional charge.








