A plug & play appliance or virtual machine - for an all-round cyber-secure IT infrastructure!
The DEFENDERBOX protects companies in all sectors with fully automated security checks of the entire IT infrastructure. The check intervals - daily, weekly, fortnightly or monthly - depend on your implementation speed.
Identified security gaps are documented in detail and prioritized. We assess the risks in the reporting and provide clear recommendations for action - for sustainable IT security and maximum protection against cyber attacks.

The DEFENDERBOX uses AI-supported attack paths & analyses to detect security vulnerabilities at an early stage.

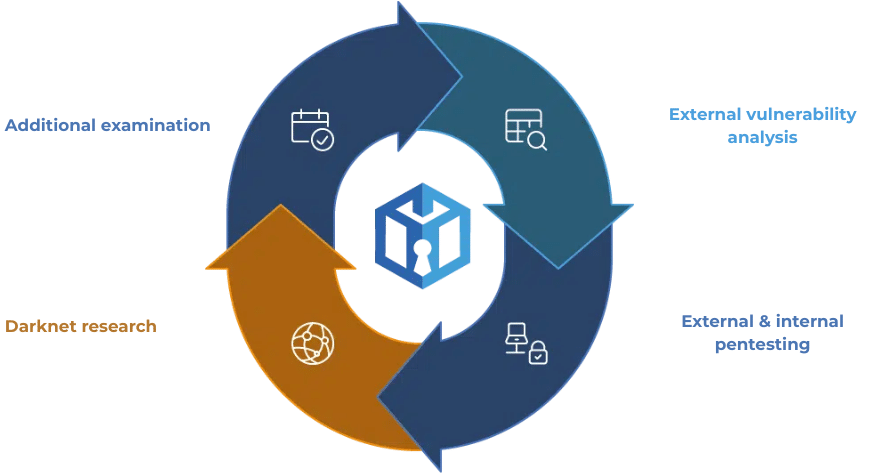
Vulnerability analysis, internal & external pentests incl. additional tests such as AD/audits, network load tests or greybox tests every 2-3 months.

The DEFENDERBOX is simply connected to the network and power supply - no IT knowledge required.

All data is processed exclusively in Germany. None of your data will be stored.

Targeted checks on the Darknet for company data, compromised email addresses and passwords.

Full control over your company data - transparent, traceable and secure.

The DEFENDERBOX evaluations are tailored to the requirements of the management and the IT department: once short & crisp - once detailed & specific!

The DEFENDERBOX provides clear recommendations for action so that security gaps can be closed quickly, in a structured and comprehensible manner.

The security gaps found are prioritized precisely. This means you know which gaps need to be closed first.

DEFENDERBOX supports companies in the structured fulfillment of increasing compliance requirements.

On-premise, multi-cloud, hybrid IT - the DEFENDERBOX moves seamlessly between environments.

NodeZero® from Horizon3.ai is part of the DEFENDERBOX! How to get world-class enterprise pentesting at an SME price.
The external vulnerability analysis scans are systematic processes in order to identify and assess deficiencies in various areas of the IT infrastructure. The main objective of a vulnerability analysis is to identify potential security gaps or inefficient processes before they can have a negative impact on the company.
The process comprises several key steps, including

The DEFENDERBOX automated external pentest is a structured testing process that aims to identify and assess security gaps in the external IT-infrastructure and proactively monitor the current security situation. The advantages such as speed, efficiency, cost-effectiveness and reproducibility come into play.
The process comprises key steps and aspects, including

The automated internal pentest is a structured process for identifying security vulnerabilities within a company network. Advantages such as efficiency, cost savings and reproducibility come into play.
The process comprises key steps and aspects, including

The Darknet research is a targeted investigation of information and activities that take place on the darknet. This type of research requires special technical knowledge and tools, as the darknet is only accessible via specific software, such as the Tor browser. In addition, the email addresses found are checked to see whether they are contained in data leaks.
The darknet research process comprises key steps and aspects:

With the DEFENDERBOX your IT infrastructure remains permanent protected - completely without additional effort. The solution is provided as a plug-and-play appliance or virtual machine and, as a managed security service, takes over the continuous Review of your systems - internally and externally.
monthly with 100 IP's
plus one-time 249€ setup fee
Everything you need to know - quickly, clearly and at a glance.
The DEFENDERBOX is your Proactive security solution to the continuous monitoring of your company network.
As a Managed Security Service recognizes them:
Before damage occurs.
Our solution is primarily aimed at Small and medium-sized enterprises (SMEs)who want to take their IT security to the next level.
The DEFENDERBOX is also particularly interesting for companies with High compliance requirementse.g:
The DEFENDERBOX delivers detailed reports and Prioritized recommendations for actionthat you can import directly into your ISMS can be integrated.
This helps you to meet the requirements of:
✅ ISO 27001/2 | ✅ TISAX | ✅ DORA | ✅ DSGVO | ✅ NIS2
to fulfill - Fast, efficient and without additional effort.
The DEFENDERBOX goes far beyond traditional antivirus or firewall solutions. While conventional software usually only detects known threats, DEFENDERBOX carries out active security checks and internal and external penetration tests that simulate real attacks. This also reveals hidden security vulnerabilities that other systems overlook because they are not designed to do so.
The DEFENDERBOX provides optimum support for your security measures: it not only protects PCs and servers, but also networked production systems, IoT devices and industry-specific software. This allows companies to benefit from holistic protection that continuously monitors, detects risks at an early stage and provides specific recommendations for action - without IT teams having to constantly check manually.
Yes - Plug & Play.
The DEFENDERBOX is preconfigured and is ready for use in just a few minutes:
No specialist IT knowledge required!
The Intuitive dashboard (coming soon) also provides a complete overview.
The DEFENDERBOX works proactive and combined:
So you can react in good time - before Attackers can cause damage.
Many SMEs have not their own Security Operations Center or a Dedicated IT department. The DEFENDERBOX closes this gap:
Do you have your own IT department? All the better!
Your experts can use the DEFENDERBOX Act immediatelyminimize risks and protect your company Proactively protect against cyberattacks.