Why your OT systems will be the new gateway for hackers in 2026
Imagine the following scenario: Your IT department has done an excellent job. Firewalls are up-to-date, emails are filtered, and employees are trained on phishing awareness. The IT network is considered secure.
But while everyone is staring at the screen on the second floor, there's an old control unit (PLC) in the production hall that hasn't been patched in years and is now communicating directly with the internet because it „needs to be remotely controlled for maintenance.“.
Welcome to the reality of IT/OT Convergence in the year 2026.
For a long time, Information Technology (IT) and Operational Technology (OT) were two separate worlds. IT dealt with data, while OT dealt with machines, valves, and robotic arms.
But Industry 4.0 and the pressure to increase efficiency have torn down these walls. Today, data flows directly from the production line into sales' ERP systems.
This is good for logistics, but a nightmare for security: The attack surface has multiplied.
Why traditional security tools fail in production
The biggest problem is not malice, but ignorance and technical incompatibility. Classic virus scanners or firewall rules that work in IT are often counterproductive in OT.
- Outdated Systems Many industrial control systems run on Windows versions that haven't received updates in a decade. A classic patch is often impossible because the manufacturer no longer supports the software.
- Sensitivity: An aggressive network scan from a conventional security tool can crash an old PLC. The „protection attempt“ thus directly leads to a production shutdown – the very scenario one was trying to prevent.
- Lateral Movement Hackers know this. They no longer primarily enter through the well-guarded production firewall. They hack the laptop in procurement, move laterally through the network, and suddenly find themselves in front of the unprotected machine control. From there, the leap to sabotage or encrypting the entire manufacturing process is only a short one.
Statistics and reports from 2025 clearly show: cyberattacks on industry are increasingly less aimed at data theft, but rather at Business interruption and extortion by shutdown. For a small or medium-sized enterprise (SME) in the manufacturing sector, even four hours of downtime can often be an existential threat.
The Solution: Visibility Without Risk
So how do you protect systems that you can't patch and can't hit with aggressive scans? The answer is: Passive analysis and special, hardware-isolated tests.
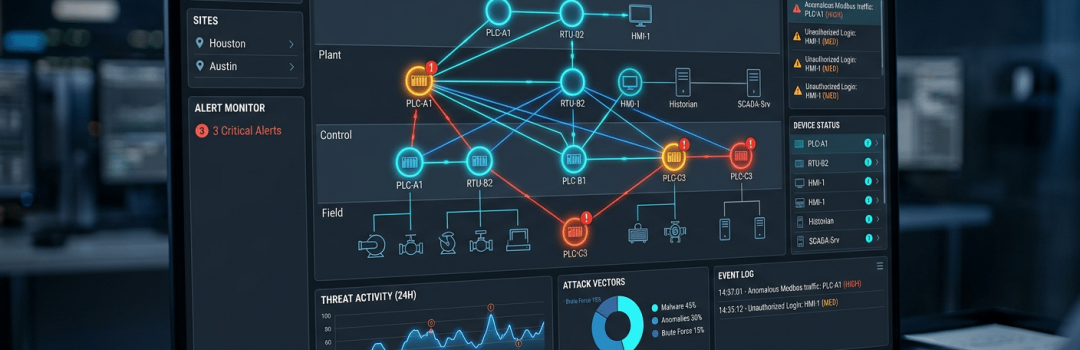
It is no longer enough to hope that the „separation“ between IT and the shop floor holds. You need a 360-degree view that encompasses both worlds without endangering production.
This is precisely where the DEFENDERBOX OT an:
Unlike pure software solutions that are installed on servers, the DEFENDERBOX OT as a physical unit in your network segment.
It enables the identification of security vulnerabilities in the OT environment, without interfere with current processes. The plug-and-play approach allows DEFENDERBOX connected to the network and automatically analyzes which devices are communicating, which ports are open, and where outdated protocols are being used. It simulates attack vectors in a way that ensures no sensitive control unit crashes, but ruthlessly uncovers the backdoors an attacker would use.
Conclusion: Don't wait for the standstill
The convergence of IT and OT is unstoppable and offers enormous opportunities. However, it makes your production a new preferred target for cybercriminals. Protection must not stop at the office door.
Invest in a solution that speaks the language of machines. A one-time check is not enough! The threat landscape changes daily. With continuous, automated monitoring of your IT & OT Infrastructure Turn the biggest risk of your digitalization into your strongest line of defense. Secure your production before the first alarm sounds on the shop floor – not after.
Are you prepared for cyber attacks?
With the DEFENDERBOX Stay one step ahead of cyber threats: Strengthen your company's resilience against hacker attacks — not just in your own environment!
Stay vigilant - your IT will stay that way with us!