Three steps to more cyber security
The ever-changing threat landscape is a labyrinth of hidden communication channels and constantly evolving tactics. Keep up and optimize your cyber resilience. Here
The ever-changing threat landscape is a labyrinth of hidden communication channels and constantly evolving tactics. Keep up and optimize your cyber resilience. Here
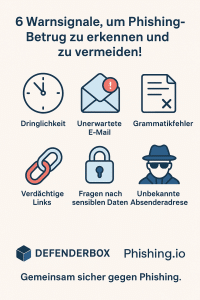
Phishing attacks have doubled since 2024 - and with AI-supported scams, they are becoming increasingly difficult to detect. But if you (re)cognize important warning signals, you can protect yourself and

DEFENDERBOX enters into a partnership with enthus - that means more protection for your company!
With advanced features, better insights and clear diagrams, automated pentesting will play a major role in the future.
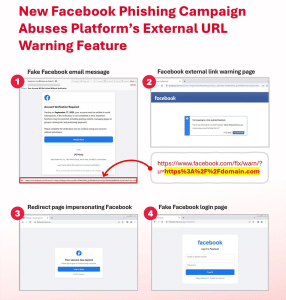
Warning: New phishing wave uses Facebook redirects to intercept credentials. Deceptively real!

In many companies, cyber security is still treated as a classic IT problem: operational, technical, selective. But this view falls short.

A significant security vulnerability was discovered in Microsoft's Copilot for M365, which allowed users to access sensitive files.

New ransomware strain also has an integrated deletion function!

When protection becomes a vulnerability - link-wrapping attacks on Microsoft 365 accounts.

Summer is the time for relaxation, travel and a change of scenery. But while many people leave everyday life behind, hackers stay active!

Vacation time also means attack time - at least from the point of view of cyber criminals.
What looks like a practical everyday tool - color selector, emoji keyboard, volume booster - can turn out to be a massive security risk.

We have successfully completed our first seed financing round!
Whether it's suspicious e-mails, unsecured WLANs or risky websites - everyone knows not to click on them!

Do you know "Scam-Yourself" - a very worrying development!
make the DEFENDERBOX trustworthy.